Development of Information Security Management System
Information is the base of business operation. If its creation, storage, handling is not safe, our business processes and ultimately our operational ability can be under threats. Deliberated management of security is essential, it may be the source of competitive advantage.
Safety is not a static state, but is rather a dynamically managed process. To comply with the challenge of a constantly changing environment, we have to review, correct and develop. Many enterprises/firms fear from it, because they do not have available capacity for doing it. But maintaining a well considered and a properly customized system does not mean extreme expenditures.
ISMS project review:
Phases of implementation:
- Situation analysis
- Exploring management needs
- Defining relevant standards
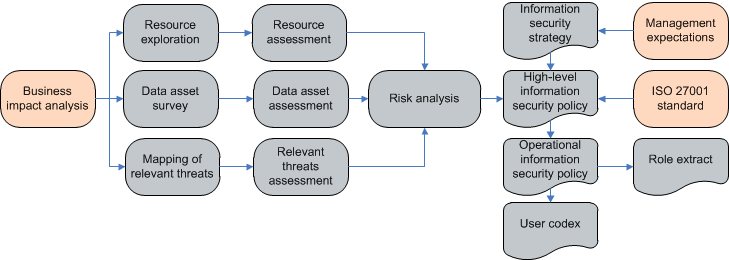
- Business impact analysis (BIA)
- IT system assessment
- Assessment of data assets
- Exploring threats
- Situation evaluation
- Reconciliation of the evaluation criteria
- Evaluation of resources
- Evaluation of data assets
- Evaluation of relevant threats
- Performing risk analysis
- Organizing protection
- Development of information security strategy
- Compilation of top-level information security regulation
- Business continuity planning (BCP – DRP)
- Development of operative procedures
- Compilation of user’s code, competence extractions
- Implementation, training
Products of this process:
- Business process data sheets
- IT system overview
- IT service catalog
- List of relevant supporting resources
- Data assets inventory
- Risk analysis report
- Risk management suggestions
- Information security strategy
- Information security framework
- Information security procedures
- User’s code
- Competence extractions


